If you plan to use unattended access, you have to think about security, as your hosts will be accessible all the time. This HowTo is for a scenario, where you don't use TeamViewer Host. I use this, because i have multiple computers from which i connect to my hosts and the other way around and therefore it doesn't make sense to use TeamViewer Host.

[1] Disable random passwords
The first and in my eyes most important step to secure unattended access is to disable the random password, especially as the default settings are very unsecure. (See [1] in the image above.)
I don't think it is needed, but i also deactivate "Random password after each session" under advanced options.
[2] Disable (all) personal password(s)
This step is optional and is only useful when the host is assigned to a TeamViewer account (see [3]). If you want to do this, do not forget, that you might have setup additional passwords. You should delete the "main" personal password ([2.1] in the above image) and any additional passwords ([2.2] in the above image).
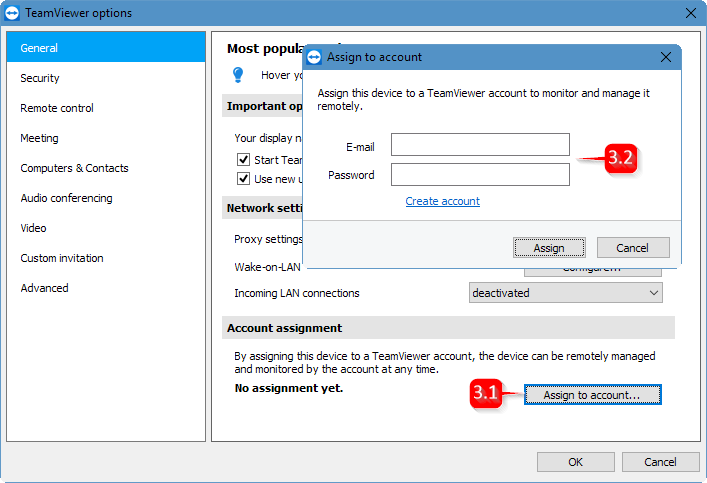
[3] Grant easy access for your account
This step in conjunction with the above steps makes unattended access most secure.
First you need to assign the computer to your TeamViewer account. You do this in TemViewer options under General at the bottom ([3.1] in the image above). In the appearing window, you have to enter your account credentials ([3.2] in the image above).
At last you have to set the checkbox "Grant <YourAccountName> easy access" ([3.3] in the image at the top). Now you can access this host without password through your account. If you have followed steps [1] and [2], it isn't possible to access this host with a TeamViewer ID / Password combination anymore.